All you need to know about the latest cybersecurity risks
The Cybersecurity landscape is ever-changing and always evolving. New threats are identified every day meaning cybersecurity professionals always need to be on their toes and ready to defend against emerging threats.
Here are three of the latest for 2019.
Cryptojacking
As defined by csoonline.com; “Cryptojacking is the unauthorized use of someone else’s computer to mine cryptocurrency. Hackers do this by either getting the victim to click on a malicious link in an email that loads crypto mining code on the computer, or by infecting a website or online ad with JavaScript code that auto-executes once loaded in the victim’s browser.” This practice is on the rise and infecting machines at an alarming rate.
Two of the most popular versions are malicious email cryptojacking and web-browser mining. With email cryptojacking, the addressee opens a seemingly-innocent email and clicks a link which downloads a script onto their computer. With web-browser mining, the hackers infect a website or an advert placed on a site with the cryptojacking script. When someone visits the site, the script is automatically executed.
With both examples, the ‘victim’ is not aware what is happening. Whilst not initially damaging, the more-powerful Cryptojacking script can impact on the ‘victims’ computer performance and even damage their machine over time.
Data Manipulation
As defined by Cloudmask, Data Manipulation is “the practice of altering digital documents and other information…in essence, hackers can infiltrate networks via any attack vector, find their way into databases and applications and change information contained in those systems, rather than stealing data and holding it for ransom.” As data is being changed as opposed to stolen, it is more likely that such actions go undetected by an organisation’s security measures and as such, can remain manipulated for some time without being rectified.
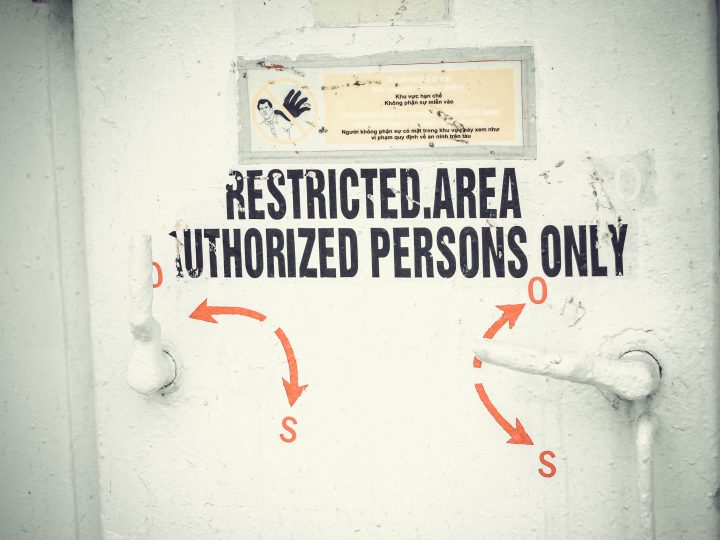
Once within the system, the cybercriminals can add unauthorised individuals to access lists for restricted areas or manipulate data for high-ranking individuals within the organisation in order to frame them. This activity could go on for months undetected and once identified would be devastating to consumer trust and data integrity within an organisation. Further to this, if the cybercriminals infiltrate something like a bank or finance institution, they would be able to manipulate bank balances and influence commercial decisions, any such actions having very detrimental effects.
The risk of IoT
IoT devices are all around us; in our homes, on our commute to work and even in our offices. Our printers, wireless routers and smart devices are all connecting to the internet simultaneously and whilst a wonderful thing, this can also pose a problem for cybersecurity professionals trying product us against the latest cybercriminal activity.
IoT devices allow industries such as manufacturing to automate processes and boost productivity allowing them to increase profits. According to a survey by BeyondTrust, 2019 is the year that IoT devices become primary targets for malware attacks. Reports published in September 2018 identified a number of key statistics including;
- There was a 29% increase in distributed denial-of-service (DDoS) attacks in the first two quarters of 2018 vs. 2017
- 93% of IoT hacks are brute-force attacks (repetitive attempts to crack a password).
- 51% of enterprises with more than 1,000 employees do not know how many devices are connected to their networks (vs. 30% within smaller organisations)
As attacks grow in frequency and severity the risk of being a target for attacks is also increasing. During 2019, it is anticipated that this trend will only continue.
There are many more risks within the cybersecurity space than those identified above. Many of which will be discussed at the global cybersecurity conferences during 2019. Are there any cybersecurity risks you think we should cover? Let us know at [email protected]